
LLMs in Cybersecurity Market Size USD 252B & 53.6% CAGR
Global Large Language Models (LLMs) in Cybersecurity Market Size, Share & AI Security Analysis By Application (Threat Detection, SOC Automation, Incident Response, Fraud Prevention), By Deployment (Cloud, On-Premise), By End User (BFSI, Government, Enterprises), Risk Landscape, Key Vendors & Forecast 2025–2034
Report Overview
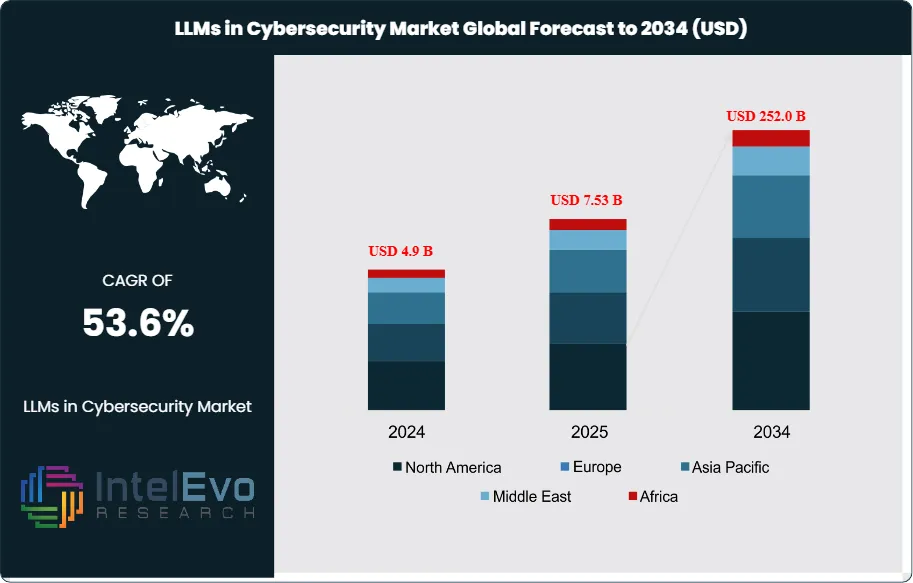
The LLMs in the Cybersecurity Market are expected to reach USD 4.9 billion in 2024. By 2034, this market could grow to around USD 252.0 billion, showing a strong compound annual growth rate of about 53.6% from 2025 to 2034. This rapid growth comes from moving AI from experiments to established uses in security operations. Companies are focusing on automated threat detection, phishing response, and incident handling as the frequency and complexity of attacks, along with regulatory demands, rise worldwide.
Get More Information about this report -
Request Free Sample ReportThe adoption of these technologies picked up speed between 2023 and 2024. Security teams progressed from pilot projects to integrating LLMs into everyday tasks. Modern models can process huge amounts of data, link unusual activities across devices and networks, and offer fixes in minutes. This greatly cuts down the time it takes to detect and respond to incidents. Spending habits are changing due to the increasing vulnerabilities that come with cloud use, remote work, and the growth of IoT, making AI-assisted security a must-have rather than just an improvement.
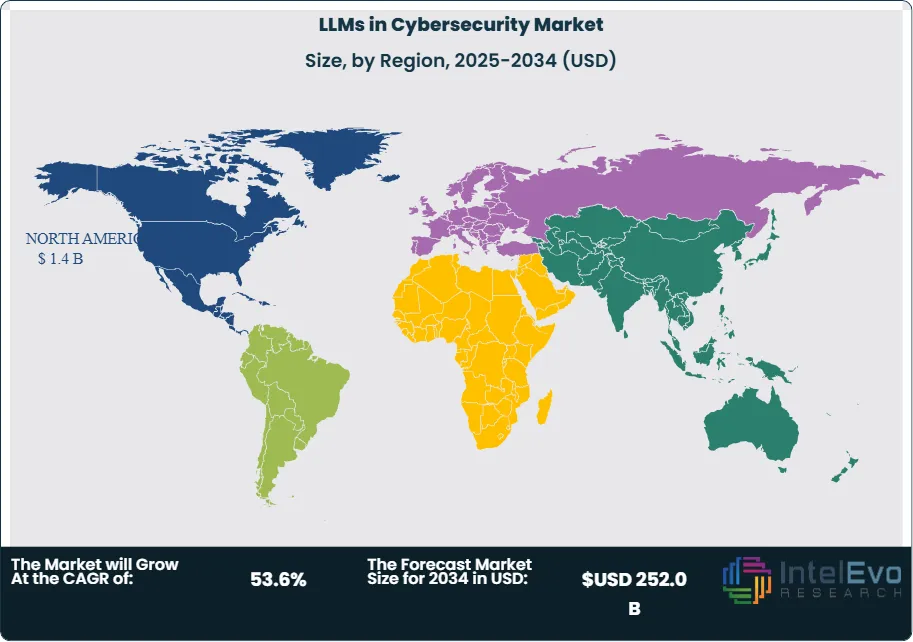
North America was the market leader in 2024, holding about 40% of the market, thanks to its developed AI systems and a strong network of cybersecurity providers. The U.S. market alone surpassed USD 1.2 billion in 2024 and keeps growing quickly. Early enterprise adoption and pressure from regulations drive this growth. Laws such as the CCPA and the New York SHIELD Act in the U.S., along with GDPR and NIS2 in Europe, are tightening accountability for breaches and increasing the need for smart, automated security measures.
On the supply side, a few leading LLM developers dominate the market, earning most of the global revenue. The level of integration is growing as LLMs become key components in systems like SIEM, SOAR, EDR, email security, and identity platforms. By 2025, many applications are expected to include LLM features, which will significantly expand both the AI attack surface and defense capabilities. Productivity improvements are considerable, with more routine security analysis and response tasks being automated through AI agents.
Even with rapid growth, risks remain. Testing shows that LLMs that are not properly tuned can struggle with accuracy in regulated settings, highlighting the need for domain-specific adjustments, augmented retrieval systems, red-teaming, and human oversight. Issues like data privacy, prompt injection, model manipulation, and vendor dependence continue to be major concerns as usage increases. Looking forward, Asia Pacific is likely to gain market share as cloud services and national cybersecurity initiatives grow in countries such as Japan, South Korea, India, and Singapore. For investors and vendors, current opportunities include secure LLMOps toolchains, frameworks for model assessment, proprietary data integration, and specialized security solutions for fields like finance, healthcare, and critical infrastructure, along with ongoing consolidation among large tech companies and cybersecurity platforms.

Key Takeaways
- Market Growth: The market reached USD 4.9 billion in 2024 and is projected to hit USD 252.0 billion by 2034 at a 53.6% CAGR, led by rapid LLM adoption in threat detection, phishing triage, and SOC automation. Rising attack complexity and AI-driven defensive investments are accelerating deployments across enterprises.
- Offering: Solutions led with 72.8% share in 2024 as buyers prioritized integrated threat detection, prevention, vulnerability management, and security automation capabilities. Tool consolidation within SIEM, SOAR, EDR, and IAM stacks is anchoring solution spend.
- Deployment: Cloud-based deployments captured 58.5% share in 2024 on flexibility, faster iteration, and API-native integrations. Large enterprises accounted for about 70% of adoption, consolidating spend in scalable, managed deployments.
- Driver: North America captured 40.7% share and USD 1.4 billion in 2024, reflecting early AI adoption and mature security stacks. Regulatory pressure, including CCPA and the New York SHIELD Act, is catalyzing advanced controls and LLM-enabled workflows
- Restraint: Market concentration is high; the top five LLM developers generated about 88.22% of global LLM revenue in 2023, heightening dependency risk on a few suppliers.
- Opportunity: BFSI led applications with 32.6% share, creating room for targeted offerings in fraud analytics, compliance, and secure communications. The U.S. market is expanding at a 49.4% CAGR from a USD 1.17 billion base in 2024, presenting strong near-term monetization.
- Trend: Network security was the top use case at 35.4% share as teams apply LLMs for anomaly detection and real-time threat analysis. Organizations are deploying LLMs for phishing and social engineering detection and to automate routine incident response tasks.
- Regional Analysis: North America led with 40.7% share and USD 1.4 billion in 2024; the U.S. alone reached USD 1.17 billion. Europe and Asia Pacific are catching up as investments ramp in AI-enhanced security from a lower base.
Offering Analysis
Solutions accounted for an estimated 72.8% share in 2024 as buyers prioritized end-to-end capabilities across threat detection and prevention, vulnerability management, security automation, data security, and identity and access management. Adoption tracked enterprise demand for tools that reduce time-to-detect and time-to-respond while scaling across high-volume telemetry and multilingual threat signals.
Services expanded as organizations sought implementation, integration, training, and ongoing support to productionize LLM use cases inside security operations; managed services gained traction where in-house expertise and 24x7 coverage remain constrained. Suppliers that package outcomes around incident triage, phishing defense, and anomaly analysis continue to gain share as enterprises consolidate point tools into integrated offerings.
By Deployment Model
Cloud-based deployments led with roughly 58.5% share in 2024, driven by elastic compute, faster iteration cycles, and API-native integrations that accelerate model updates and enterprise rollouts. Buyers favored opex-based consumption to align spend with usage while enabling rapid scale-up during attack surges or proof-of-concept expansions.
On-premises remained relevant for data sovereignty and low-latency use cases, but the center of gravity shifted to cloud platforms that bundle model hosting, guardrails, and observability for LLM workflows in security stacks. As teams standardize on cloud pipelines, update velocity and model governance improved, supporting the market’s projected 52.8% CAGR through 2034.
Organization Size Analysis
Large enterprises captured over 70% share in 2024 as regulated sectors funded advanced AI defenses to handle complex risks, audit trails, and stringent reporting requirements. These organizations deploy LLMs to parse massive event streams, surface anomalies, and assist analysts with prioritized response at scale.
Budget concentration and compliance obligations in finance, healthcare, government, and critical infrastructure accelerated upgrades to enterprise-grade models, toolchains, and evaluation frameworks. Vendors that align to enterprise controls and SIEM/SOAR workflows continue to outperform in competitive wins and expansions.
Application Analysis
Network security led with about 35.4% share in 2024 as organizations applied LLMs to detect anomalies in real time, triage alerts, and interpret complex patterns across hybrid networks. The use of LLMs in phishing and social engineering detection supported measurable reductions in false positives and analyst workload.
Adoption also advanced in endpoint, application, and cloud security, where LLMs improved root-cause narration, policy recommendations, and response playbooks at scale. As IoT growth widens the attack surface, cross-domain signal correlation remains a priority, reinforcing spend in LLM-enhanced monitoring and preemptive controls.
End-User Industry
BFSI held around 32.6% share in 2024, reflecting high exposure to fraud, payment risk, and targeted phishing that benefit from LLM-driven anomaly detection and investigative summarization. Compliance reporting and audit automation further support LLM use in regulated workflows.
Healthcare, IT and telecom, government and defense, and retail advanced deployments focused on data privacy, access governance, and faster incident response in multi-cloud environments. Manufacturing and energy emphasized operational continuity and multilingual support for global plants and supply chains using LLM-enabled threat intelligence.
Regional Analysis
North America led with 40.7% share and approximately USD 1.4 billion revenue in 2024, underpinned by mature AI ecosystems, vendor density, and enterprise-scale security modernization; the U.S. reached about USD 1.17 billion and is expanding at roughly 49.4% CAGR. Consolidation between security platforms and hyperscale AI providers remains a regional growth catalyst.
Europe and Asia Pacific are scaling from a lower base as cloud adoption, national cyber programs, and SOC modernization drive procurement cycles; the global market is projected to rise from USD 3.6 billion in 2024 to USD 249.8 billion by 2034 at a 52.8% CAGR, reinforcing a multi-region expansion path. Market concentration remains elevated, with the top five LLM developers accounting for about 88.22% of revenue in 2023, shaping access and pricing globally.
Get More Information about this report -
Request Free Sample ReportMarket Key Segments
By Offering
- Solutions
- Threat Detection and Prevention
- Vulnerability Management
- Security Automation
- Data Security
- Identity and Access Management
- Others
- Services
- Professional Services
- Implementation & Integration Services
- Consulting & Training
- Support & Maintenance
- Managed Services
- Professional Services
By Deployment Model
- Cloud-based
- On-premises
By Organization Size
- Large Enterprises
- Small and Medium-sized Enterprises (SMEs)
By Application
- Network Security
- Endpoint Security
- Application Security
- Cloud Security
- Others
By End-User Industry
- Banking, Financial Services, and Insurance (BFSI)
- Healthcare
- IT & Telecom
- Government and Defense
- Retail
- Manufacturing
- Others (Aerospace, & Energy and Utilities, etc.)
Regions
- North America
- Latin America
- East Asia And Pacific
- Sea And South Asia
- Eastern Europe
- Western Europe
- Middle East & Africa
| Report Attribute | Details |
| Market size (2024) | USD 4.9 B |
| Forecast Revenue (2034) | USD 252.0 B |
| CAGR (2024-2034) | 53.6% |
| Historical data | 2020-2023 |
| Base Year For Estimation | 2024 |
| Forecast Period | 2025-2034 |
| Report coverage | Revenue Forecast, Competitive Landscape, Market Dynamics, Growth Factors, Trends and Recent Developments |
| Segments covered | By Offering (Solutions, Services), By Deployment Model (Cloud-based, On-premises), By Organization Size (Large Enterprises, Small and Medium-sized Enterprises (SMEs)), By Application (Network Security, Endpoint Security, Application Security, Cloud Security, Others), By End-User Industry (Banking, Financial Services, and Insurance (BFSI), Healthcare, IT & Telecom, Government and Defense, Retail, Manufacturing, Others (Aerospace, & Energy and Utilities, etc.)), |
| Research Methodology |
|
| Regional scope |
|
| Competitive Landscape | Fortinet, Inc., CyberArk Software Ltd., Splunk Inc., Lasso.security, CrowdStrike, International Business Machines Corporation (IBM), Darktrace Holdings Ltd, Broadcom, Cisco Systems, Inc., Zscaler, Inc., Palo Alto Networks, Inc., Vectra AI, Inc., Others |
| Customization Scope | Customization for segments, region/country-level will be provided. Moreover, additional customization can be done based on the requirements. |
| Pricing and Purchase Options | Avail customized purchase options to meet your exact research needs. We have three licenses to opt for: Single User License, Multi-User License (Up to 5 Users), Corporate Use License (Unlimited User and Printable PDF). |
Select Licence Type
Connect with our sales team
LLMs in Cybersecurity Market
Published Date : 25 Dec 2025 | Formats :Why IntelEvoResearch
100%
Customer
Satisfaction
24x7+
Availability - we are always
there when you need us
200+
Fortune 50 Companies trust
IntelEvoResearch
80%
of our reports are exclusive
and first in the industry
100%
more data
and analysis
1000+
reports published
till date







