
Security Market to Reach USD 345.26 Bn by 2034 | CAGR of 8.40%
Global Security Market Size, Share, Analysis Report By System (Barrier, Access Control, Intrusion Detection, Alarms & Notification, Video Surveillance) Service (Managed Security Services, System Integration & Consulting - leads, Risk Assessment & Analysis, Maintenance and Support) End-use (Industrial, Government, Transportation, Military & Defence - leads, Commercial) Industry Region & Key Players-Industry Segment Overview, Market Dynamics, Competitive Strategies, Trends & Forecast 2025-2034
Report Overview
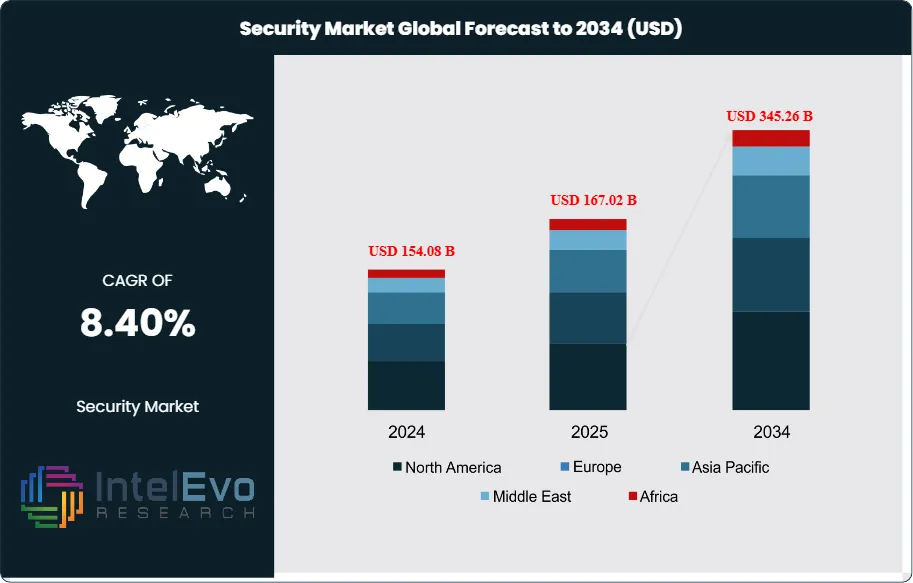
The Security Market size is expected to be worth around USD 345.26 billion by 2034, rising from USD 154.08 billion in 2024, and expanding at a CAGR of 8.40% during the forecast period from 2024 to 2034. This growth is driven by rising cyber threats, increasing adoption of cloud computing, and growing demand for advanced security solutions across enterprises and governments. The rapid integration of AI, machine learning, and zero-trust architectures is further transforming security strategies, positioning the market as a critical pillar for protecting digital assets and critical infrastructure worldwide.
Get More Information about this report -
Request Free Sample ReportThe security market has emerged as a critical component of the global economy, addressing escalating concerns around physical safety, cybersecurity, and data protection. The market encompasses a comprehensive range of solutions including surveillance systems, access control, intrusion detection, cybersecurity tools, biometrics, and integrated solutions powered by artificial intelligence and Internet of Things technologies. These innovations enhance real-time threat detection, streamline responses, and provide predictive analytics to prevent incidents before they occur.
Market expansion is driven by increasing illegal events, terrorism, fraudulent activities globally, and stringent government norms that have accelerated adoption of security systems. The security industry benefits from significant adoption rates in military & defense sectors due to increased terrorism threats and cross-border intrusions. As global economies become more interconnected and dependent on digital infrastructure, demand for advanced security solutions has surged across residential, commercial, industrial, and governmental sectors.
The COVID-19 pandemic has further underscored the importance of physical security as organizations reassess their safety protocols to protect employees and visitors in an increasingly uncertain environment. Additionally, regulatory frameworks such as GDPR in Europe and CCPA in California have compelled organizations to prioritize security measures to avoid hefty penalties.
Regional market dynamics show North America leading with advanced technological infrastructure and significant investments in security solutions, particularly in the U.S. with strong demand across government, military, commercial, and industrial sectors. Increasing cyber threats, high-profile data breaches, and terrorism concerns have prompted businesses and governments to prioritize security.
Trade tensions and geopolitical conflicts have heightened the need for robust security infrastructure, particularly in critical sectors like defense, telecommunications, and energy. Organizations are investing heavily in securing supply chains and protecting against state-sponsored cyber-attacks.

Key Takeaways
- Market Size & Growth: The Security Market is expected to reach USD 345.26 Billion by 2034, driven by escalating security threats and evolving technological demands across multiple sectors.
- System Type Dominance: Video Surveillance Systems lead because they provide comprehensive visual monitoring with advanced AI-powered analytics, real-time threat detection, and scalable solutions that address growing security concerns across all industries.
- Service Type Dominance: System Integration & Consulting leads in services due to the critical demand for unified security platforms that centralize multiple security components and provide customized solutions.
- End User Dominance: Military & Defence dominates end-use applications because governments worldwide prioritize modernizing defense capabilities to counter emerging threats like cyber warfare and terrorism.
- Drivers: Key drivers accelerating growth include increasing cyber threats and terrorism concerns, which boost market expansion through heightened security awareness and regulatory compliance requirements.
- Restraints: Growth is hindered by high implementation costs and lack of skilled personnel, which create challenges such as budget constraints for smaller businesses and operational difficulties.
- Opportunities: The market is poised for expansion due to opportunities like AI integration and IoT adoption, which enable enhanced threat detection and predictive analytics capabilities.
- Trends: Emerging trends including cloud migration and remote monitoring are reshaping the market by enabling scalable, real-time protection and mobile security applications.
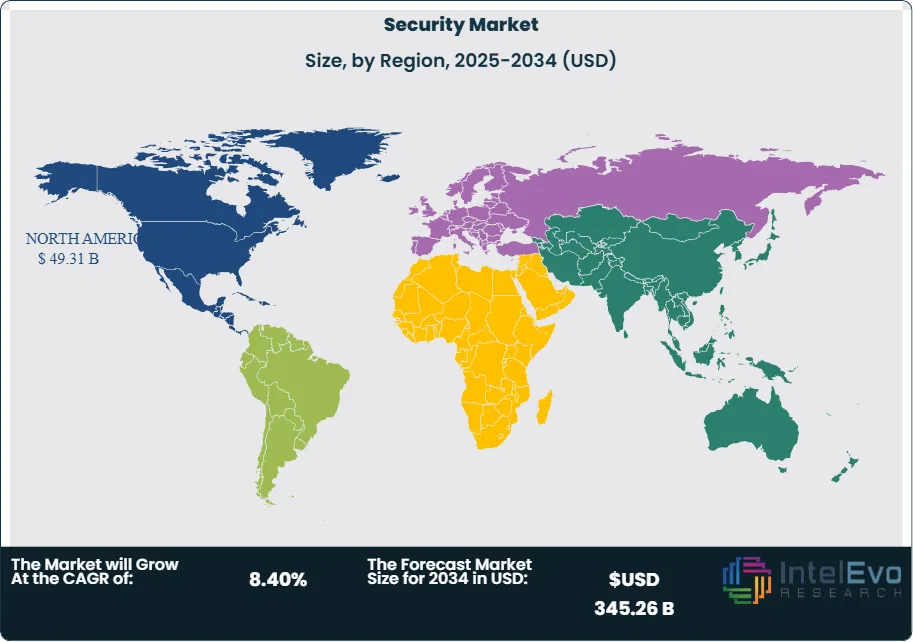
- Regional Analysis: North America leads owing to advanced technological infrastructure and significant security investments. Asia Pacific shows high promise due to rapid industrialization and growing cybersecurity concerns.
System Type Analysis:
Video Surveillance Systems Leads With over 45% Market Share In Security Market: The video surveillance systems segment's leadership position stems from its technological sophistication and universal applicability across sectors. Modern surveillance systems incorporate artificial intelligence for facial recognition, behavioral analysis, and automated threat detection, making them indispensable for proactive security management. Their integration capabilities with other security components and cloud-based accessibility have made them the cornerstone of comprehensive security strategies for retail, transportation, banking, and government facilities.
Service Type Analysis:
System integration and consulting services dominate because organizations increasingly require holistic security solutions rather than fragmented systems. Professional integrators eliminate security vulnerabilities by creating seamless connections between physical security, cybersecurity, and operational systems. Their expertise ensures optimal system performance, reduces operational complexity, and provides ongoing strategic guidance for evolving security needs.
End User Analysis:
The military and defense end-use segment's prominence reflects global security imperatives and substantial government investments in advanced protection technologies. Defense organizations require sophisticated surveillance systems, secure communication networks, and electronic warfare capabilities to maintain operational superiority against evolving threats including terrorism, espionage, and border security challenges.
Regional Analysis:
North America Leads With more than 30% Market Share In Security Market: North America dominates the global security market with a 32% market share in 2024, primarily driven by the United States' advanced technological infrastructure and substantial security investments across government, military, commercial, and industrial sectors. The region benefits from stringent regulatory frameworks, high digital penetration rates, and early adoption of cutting-edge technologies such as AI, IoT, and cloud-based security systems. Increasing cyber threats, high-profile data breaches, and terrorism concerns have prompted both businesses and governments to prioritize comprehensive security solutions.
Europe represents the second-largest regional market, characterized by strict data protection regulations like GDPR that compel organizations to invest heavily in security infrastructure. The region shows strong adoption of integrated security solutions and advanced surveillance technologies. Asia Pacific emerges as the fastest-growing region, fueled by rapid industrialization, urbanization, and growing cybersecurity awareness. Countries like China and India are experiencing significant demand growth due to expanding digital economies and increasing security threats.
Latin America and Middle East & Africa regions present substantial growth opportunities, driven by infrastructure development, rising security concerns, and government initiatives to modernize security systems. These emerging markets are gradually adopting advanced security technologies as economic conditions improve and threat landscapes evolve.
Get More Information about this report -
Request Free Sample ReportKey Market Segment
System
- Barrier Systems
- Access Control Systems
- Intrusion Detection Systems
- Alarms & Notification Systems
- Video Surveillance Systems - leads
- Others
Service
- Managed Security Services
- System Integration & Consulting - leads
- Risk Assessment & Analysis
- Maintenance and Support
End-use
- Industrial
- Government
- Transportation
- Military & Defence - leads
- Commercial
- Others
Region:
- North America
- Latin America
- East Asia And Pacific
- Sea And South Asia
- Eastern Europe
- Western Europe
- Middle East & Africa
| Report Attribute | Details |
| Market size (2025) | USD 167.02 B |
| Forecast Revenue (2034) | USD 345.26 B |
| CAGR (2025-2034) | 8.40% |
| Historical data | 2018-2023 |
| Base Year For Estimation | 2024 |
| Forecast Period | 2025-2034 |
| Report coverage | Revenue Forecast, Competitive Landscape, Market Dynamics, Growth Factors, Trends and Recent Developments |
| Segments covered | System (Barrier Systems, Access Control Systems, Intrusion Detection Systems, Alarms & Notification Systems, Video Surveillance Systems - leads, Others) Service (Managed Security Services, System Integration & Consulting - leads, Risk Assessment & Analysis, Maintenance and Support) End-use (Industrial, Government, Transportation, Military & Defence - leads, Commercial, Others) |
| Research Methodology |
|
| Regional scope |
|
| Competitive Landscape | Apex Fabrication & Design, Inc., Johnson Controls, ASSA ABLOY, Axis Communications AB, Perimeter Protection Germany GmbH, Honeywell International, Inc., ZABAG Security Engineering GmbH, Teledyne FLIR LLC, Apex Perimeter Protection, Anixter Inc. |
| Customization Scope | Customization for segments, region/country-level will be provided. Moreover, additional customization can be done based on the requirements. |
| Pricing and Purchase Options | Avail customized purchase options to meet your exact research needs. We have three licenses to opt for: Single User License, Multi-User License (Up to 5 Users), Corporate Use License (Unlimited User and Printable PDF). |
Select Licence Type
Connect with our sales team
Why IntelEvoResearch
100%
Customer
Satisfaction
24x7+
Availability - we are always
there when you need us
200+
Fortune 50 Companies trust
IntelEvoResearch
80%
of our reports are exclusive
and first in the industry
100%
more data
and analysis
1000+
reports published
till date







